NGINX Just Patched an 18-Year-Old Bug That Gives Attackers Remote Code Execution
NGINX Just Patched an 18-Year-Old Bug That Gives Attackers Remote Code Execution
Somewhere in your infrastructure, there’s almost certainly an NGINX server. It’s been quietly, reliably handling your traffic for years. And for 18 of those years, it’s been carrying a critical memory corruption bug that lets anyone with network access execute code remotely.
CVE-2026-42945 — discovered by DepthFirst Labs and disclosed on May 13, 2026 — is a heap buffer overflow in NGINX’s ngx_http_rewrite_module that dates all the way back to version 0.6.27, released in 2008. It carries a CVSS v4 score of 9.2 (Critical) and a CVSS v3.1 score of 8.1 (High). And there’s already a public proof-of-concept exploit on GitHub.
Eighteen years. Every NGINX version from 2008 to last week is affected.
What Happened
The vulnerability lives in NGINX’s URL rewriting engine — specifically in how the ngx_http_rewrite_module handles PCRE regex captures (like $1, $2) in rewrite replacement strings that contain a question mark (?).
Here’s the trigger condition. If your NGINX config contains something like this:
rewrite ^/old/(.*)$ /new/$1?param=value;
rewrite ^/some/other/path$ /destination;
# OR: if ($condition) { ... }
# OR: set $variable "value";…then you’re vulnerable. The first rewrite uses an unnamed capture ($1) in a replacement string containing ?, and it’s followed by another rewrite, if, or set directive. That’s the pattern.
When this pattern is present, an unauthenticated attacker can send a crafted HTTP request with a malicious URI. NGINX’s rewrite engine computes the buffer size using one set of escaping assumptions, then writes to that buffer using a different set. The write overflows the heap buffer with attacker-controlled data.
Why It’s Serious
Deterministic, Not Probabilistic
This isn’t one of those vulnerabilities where the attacker has to get lucky with a race condition or brute-force memory addresses. The heap corruption is deterministic — the same crafted URI reliably produces the same overflow every single time. That makes it significantly easier to exploit.
From DoS to RCE
At minimum, successful exploitation crashes the NGINX worker process (denial of service). But on systems where Address Space Layout Randomization (ASLR) is disabled — which is more common than you’d think, especially in embedded devices, containers with specific configurations, or older deployments — the bug enables full remote code execution.
The public PoC demonstrates exactly this: using cross-request heap feng shui to corrupt an adjacent memory pool’s cleanup pointer, then redirecting it to execute system() on pool destruction. Pop a shell. Game over.
The Config Pattern Is Common
URL rewriting with regex captures is bread-and-butter NGINX configuration. It’s used for SEO redirects, legacy URL migration, API routing, and dozens of other common patterns. This isn’t some obscure misconfiguration — it’s how people actually use NGINX.
The Technical Bit (For Those Who Want the Details)
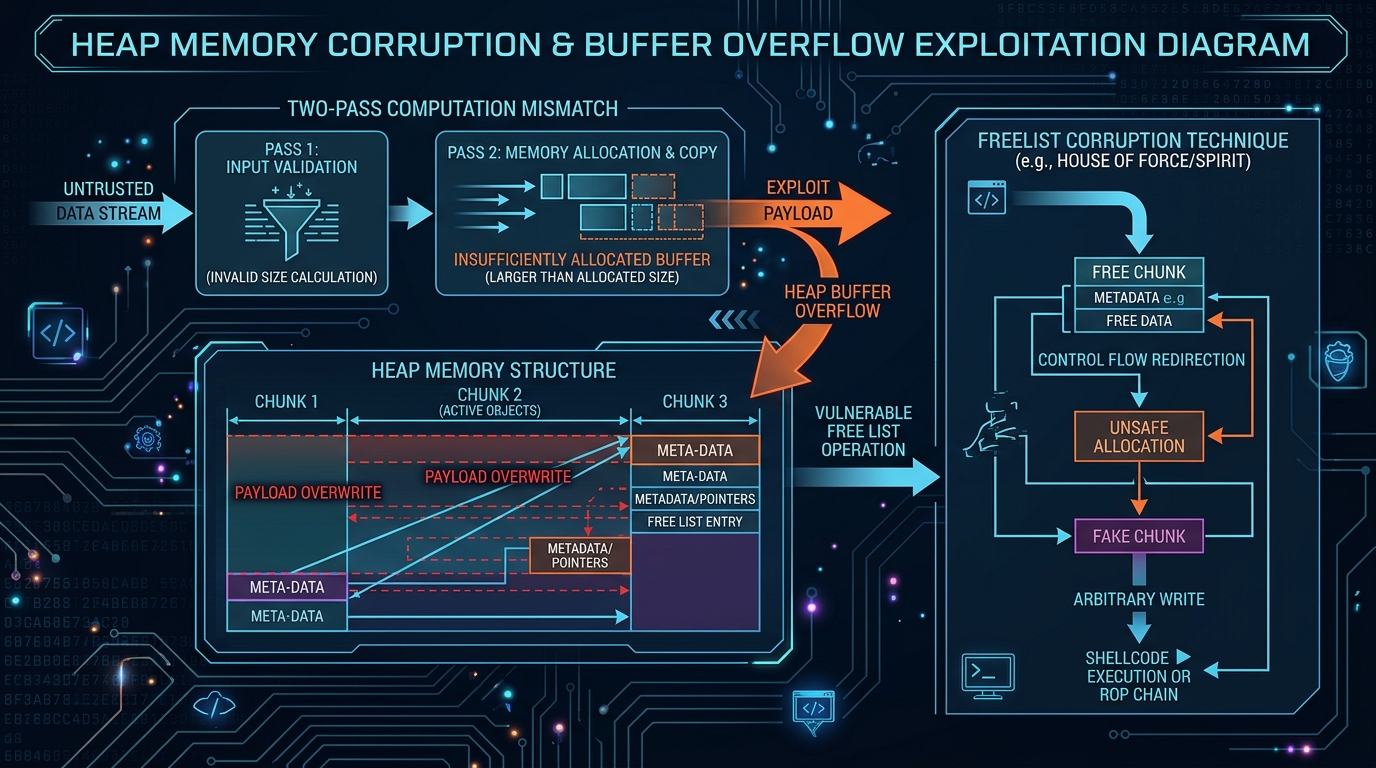
The bug is a beautiful example of a two-pass computation mismatch. Here’s how it works:
NGINX’s script engine processes rewrite replacements in two passes:
- The length pass — computes how much buffer space the output will need
- The copy pass — actually writes the data into the allocated buffer
The problem centers on a flag called is_args, which gets set on the main script engine when a rewrite replacement string contains ?. This flag tells the copy pass to URI-escape the captured value (since it’s going into a query string), expanding certain characters from 1 byte to 3 bytes (e.g., %XX encoding).
But here’s the critical detail: when a second rewrite, if, or set directive runs, it creates a freshly zeroed sub-engine. The length calculation pass runs on this sub-engine — where is_args = 0. The copy pass, however, inherits is_args = 1 from the parent engine.
Result:
- Length pass sees
is_args = 0→ calculates raw capture length (no escaping) - Copy pass sees
is_args = 1→ callsngx_escape_uriwithNGX_ESCAPE_ARGS, expanding each escapable byte to 3 bytes
The copy writes significantly more data than the length pass allocated. Heap buffer overflow. Deterministic. Attacker controls the URI content.
The DepthFirst Labs PoC exploits this by using cross-request heap feng shui — spraying the heap with controlled data via POST bodies (since URI bytes can’t contain null bytes) — to corrupt an adjacent ngx_pool_t cleanup pointer. When the pool is destroyed, the corrupted pointer redirects execution to a fake cleanup structure that calls system(). Shell obtained.
Who’s Affected
NGINX Open Source: versions 0.6.27 through 1.30.0 (basically everything from 2008 to May 2026)
NGINX Plus: releases R32 through R36, Instance Manager 2.16.0–2.21.1, F5 WAF for NGINX 5.9.0–5.12.1
Kubernetes Ingress-NGINX: affected — update to v1.13.7+ or v1.14.3+
NGINX powers roughly a third of all websites on the internet. The reach of this vulnerability is massive.
How to Check If You’re Vulnerable
1. Check your NGINX version:
nginx -vIf it’s anything below 1.30.1 (stable) or 1.31.0 (mainline), you’re potentially affected.
2. Check your configuration for the vulnerable pattern:
grep -r "rewrite" /etc/nginx/ | grep '\$[0-9]' | grep '?'Look for rewrite directives that use captures like $1, $2 etc. in replacement strings containing ?, followed by another rewrite, if, or set directive.
3. Verify ASLR status (Linux):
cat /proc/sys/kernel/randomize_va_spaceIf it returns 0, ASLR is disabled and you’re at risk for full RCE. If 2, ASLR is enabled (still vulnerable to DoS, RCE is harder but not impossible).
What You Should Do — Right Now
Immediate (today):
- Upgrade NGINX to 1.30.1 (stable) or 1.31.0 (mainline) — these are the patched versions
- If you’re running NGINX Plus, patch to the latest release (R37 or the appropriate patch level for your branch)
- If you’re running Kubernetes Ingress-NGINX, update to v1.13.7+ or v1.14.3+
- Check your package manager — many distros have backported patches. Ubuntu, Debian, RHEL, and others have likely issued updates even if the version number doesn’t match
Short-term (1–3 days):
- If you can’t patch immediately, refactor your NGINX configs to avoid the vulnerable pattern — remove the
?from capture replacement strings, or restructure to avoid having arewrite/if/setdirective after a rewrite with captures - Ensure ASLR is enabled on all NGINX servers — while this doesn’t eliminate the vulnerability, it significantly raises the bar for RCE exploitation
- Review access logs for unusual or malformed URIs that might indicate exploitation attempts
Longer term:
- Also patch the related CVEs fixed in the same release:
- CVE-2026-42926 — HTTP/2 request injection via
ngx_http_proxy_module - CVE-2026-42946 — Buffer overread in SCGI/UWSGI modules
- CVE-2026-42934 — Buffer overread in charset module
- CVE-2026-40460 — HTTP/3 address spoofing
- CVE-2026-40701 — Use-after-free in OCSP requests
- CVE-2026-42926 — HTTP/2 request injection via
- Audit your NGINX configurations regularly. Rewrite rules are one of the most complex parts of NGINX config — and complexity is where bugs hide
- Run vulnerability scans against your NGINX infrastructure to catch unpatched instances
The Bigger Story: Found by AI, Again
Here’s something that should sound familiar by now. DepthFirst Labs reports that this vulnerability — along with three other memory corruption issues in the same release — was autonomously discovered by their security analysis system after a single click to onboard the NGINX source code.
This is the second major vulnerability we’ve covered this month that was found by automated security analysis tools. First Copy Fail (CVE-2026-31431) was surfaced by Theori’s Xint Code in about an hour. Now NGINX Rift (CVE-2026-42945) was found by DepthFirst’s autonomous system.
The pattern is clear: the era of bugs lurking in critical infrastructure for decades is accelerating toward its end — not because humans are getting better at code review, but because machines are getting better at finding what humans missed.
The Bottom Line
CVE-2026-42945 is an 18-year-old critical heap buffer overflow in NGINX’s rewrite module that enables unauthenticated remote code execution on servers with a common configuration pattern. A public proof-of-concept exploit exists. Patch to NGINX 1.30.1 or 1.31.0 immediately. If you can’t patch today, refactor your configs. And while you’re at it, check if you’ve been running the same NGINX version since the Obama administration — it might be time for a broader security review.

