1.5 Million Servers, Zero Passwords: The cPanel Auth Bypass Targeting Governments
1.5 Million Servers. A CVSS 9.8 Bug. Zero Authentication Required.
If your hosting provider runs cPanel — and statistically, there’s a good chance they do — you need to read this right now. Not later. Not after coffee. Now.
CVE-2026-41940 is a critical pre-authentication remote authentication bypass in cPanel & WHM, the web hosting control panel that powers roughly 1.5 million internet-facing servers. It carries a CVSS score of 9.8 out of 10, which in plain English means: anyone on the internet can log into your server as root without a password.
And it’s already being exploited. Not by random script kiddies — by actors targeting government agencies and military infrastructure in Southeast Asia.
What Happened
On April 28, 2026, cPanel issued an emergency security patch for what their release notes modestly described as “an issue with session loading and saving.” The reality is considerably more alarming.
The vulnerability, discovered and analyzed by security firm watchTowr, is a pre-authentication authentication bypass that chains together three separate weaknesses in how cPanel handles login sessions. The result: an unauthenticated attacker can craft a malicious request that injects arbitrary data into their session file, including the magical field successful_internal_auth_with_timestamp — which tells cPanel “this user is already authenticated, skip the password check.”
By April 29, a proof-of-concept exploit was public. Within 24 hours, threat actors were deploying Mirai botnets and ransomware on compromised servers. By May 1, CISA had added it to its Known Exploited Vulnerabilities catalog.
Who’s Being Targeted
Here’s where this stops being a generic vulnerability story and becomes a genuine geopolitical concern.
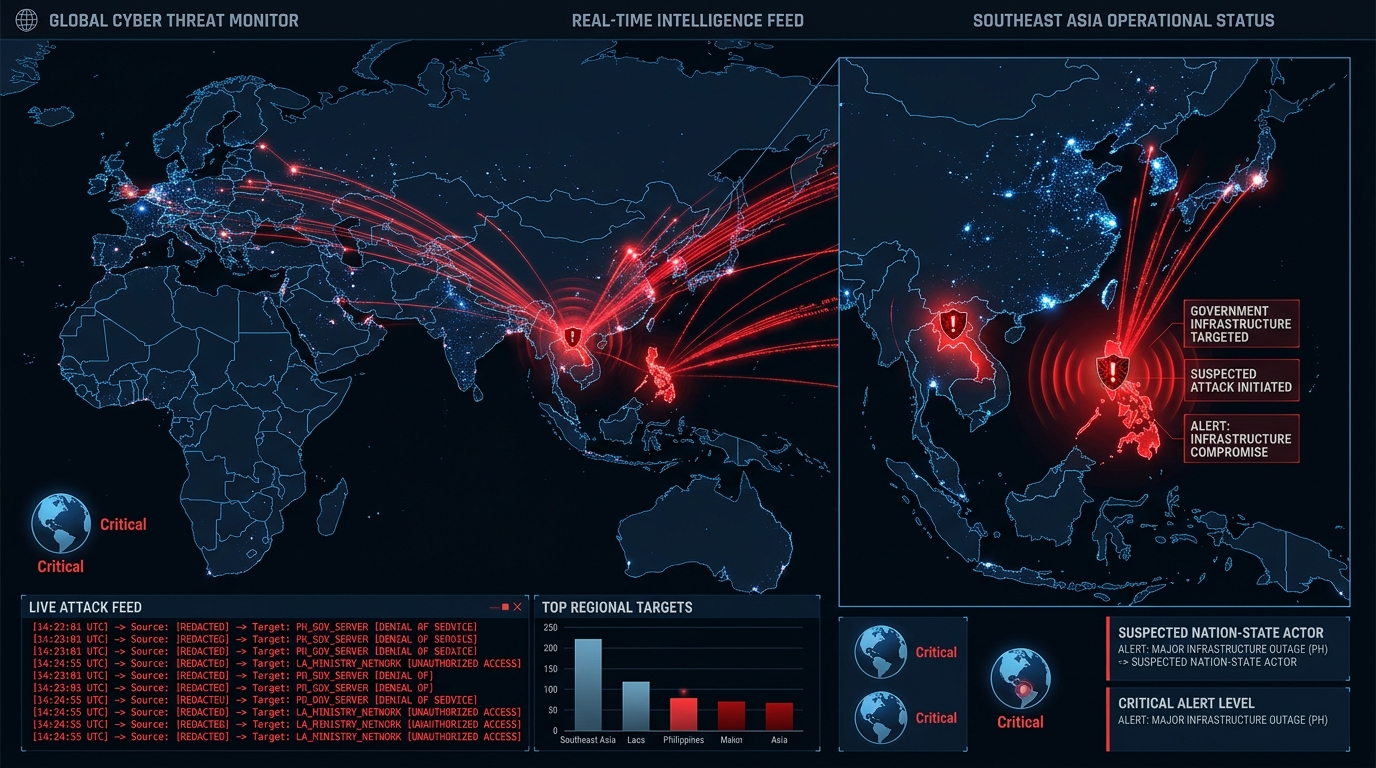
On May 2, 2026, threat intelligence firm Ctrl-Alt-Intel identified a targeted campaign exploiting CVE-2026-41940 against:
- Philippine government and military domains (*.mil.ph, *.ph)
- Laotian government infrastructure (*.gov.la)
- Managed Service Providers (MSPs) in the Philippines, Laos, Canada, South Africa, and the United States
- Hosting providers running cPanel across multiple regions
The attackers, operating from IP address 95.111.250.175, used publicly available proof-of-concept code to gain initial access, then deployed a sophisticated post-exploitation toolkit:
- AdaptixC2 — for command and control communications
- OpenVPN and Ligolo — for persistence and lateral movement across networks
- systemd services — for durable backdoor installation
In one confirmed case, attackers exfiltrated sensitive Chinese railway documents. A separate attack chain against an Indonesian defense portal combined the cPanel exploit with authenticated SQL injection and remote code execution. This isn’t opportunistic scanning — it’s a coordinated intelligence operation.
The Technical Bit (For Those Who Want Details)
The vulnerability is a masterclass in chaining small bugs into catastrophic results. Here’s the three-step exploit chain:
Step 1: CRLF Injection. The attacker sends a Basic Auth request with newline characters embedded in the credentials. By crafting the whostmgrsession cookie without the encryption-key segment, they bypass the encryption that would normally protect the session file. The cPanel daemon (cpsrvd) writes the attacker’s unsanitized input directly to disk.
Step 2: Race Condition in Session Storage. cPanel stores sessions in both a raw text file and a JSON cache. The attacker triggers a “token denied” handler, which forces the server to re-parse the poisoned raw file. The injected data gets promoted into the active session cache as if it were legitimate.
Step 3: Authentication Flag Bypass. The password-checking function (docheckpass_whostmgrd) short-circuits if the session contains a successful_internal_auth_with_timestamp field — a flag meant for legitimate internal SSO operations that has no cryptographic binding. The attacker injects this field. The system skips password verification entirely.
The whole thing is pre-authentication, requires no user interaction, and works remotely over the network. Hence the 9.8 CVSS score.
Why This Matters for Everyone — Not Just Governments
You might be thinking, “I’m not a Southeast Asian government, this doesn’t affect me.” Think again.
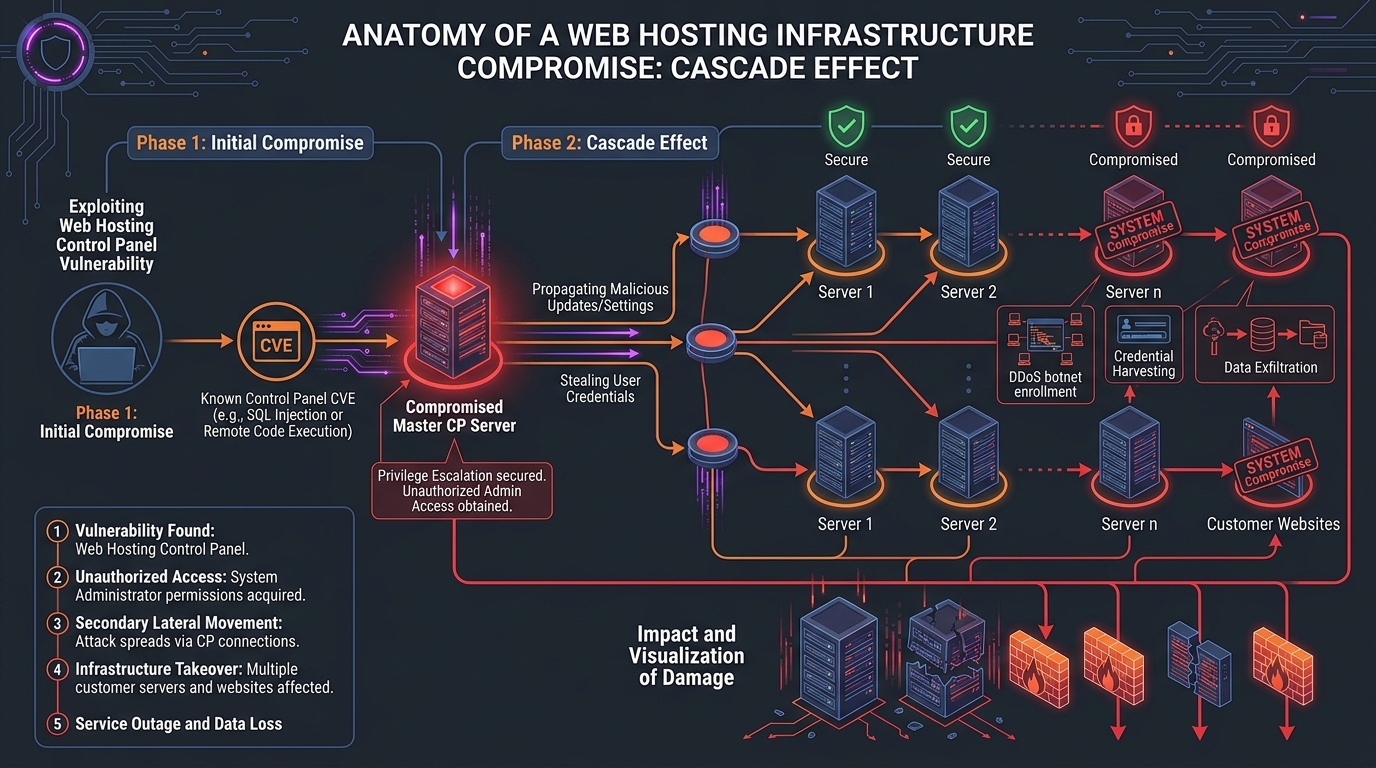
Here’s the uncomfortable math: ~1.5 million cPanel instances are exposed to the internet. Every shared hosting provider, every small business running their own server, every agency managing client websites through WHM — they’re all in the blast radius.
Even if you’re not the primary target, the fallout is massive:
- If your hosting provider gets compromised, every website they manage is at risk — including yours
- If your MSP gets hit, your entire business infrastructure could be exposed
- Mirai botnet operators are already using this to build zombie armies from compromised servers
- “Sorry” ransomware has been deployed on exploited systems within 24 hours of the PoC going public
On April 30 alone, Shadowserver detected 44,000 compromised IPs actively scanning and brute-forcing honeypots. That number dropped to 3,540 by May 3 — but that’s not a sign the threat is fading. It means the initial wave of mass exploitation succeeded, and those servers are now weaponized.
What You Should Do — Right Now
Immediate actions (today):
- Update cPanel immediately. Patches were released April 28, 2026. Check your version against the fixed releases:
- v11.86.0.41 or later
- v11.110.0.97 or later
- v11.118.0.63 or later
- v11.126.0.54 or later
- v11.130.0.19 or later
- v11.132.0.29 or later
- v11.134.0.20 or later
- v11.136.0.5 or later
- WP Squared v136.1.7 or later
- Rotate all credentials — cPanel/WHM passwords, API tokens, database passwords, everything
- Invalidate all active sessions — force every user to re-authenticate
Short-term (1–3 days):
- Audit session directories — inspect
/usr/local/cpanel/sessionfor anomalies: injected authentication timestamps, sessions with authenticated attributes but no login history, password fields with embedded newlines - Check logs for exploitation going back to February 23, 2026 — this was being exploited as a zero-day for two months before the patch
- Review network traffic for connections to known C2 infrastructure (AdaptixC2 indicators) and suspicious VPN/Ligolo tunnels
- If you’re a hosting provider, consider temporarily restricting ports 2082–2087 and 2095–2096 if you can’t patch immediately — but understand this is a workaround, not a fix
Longer term:
- Verify your hosting providers have patched. If you use shared hosting or a managed provider, ask them directly. Don’t assume
- Monitor for lateral movement — if cPanel was compromised, assume the attackers moved deeper into your infrastructure
- Review your attack surface — if WHM or cPanel ports are exposed to the entire internet, ask yourself if they need to be. Consider IP allowlisting or VPN-only access
The Bottom Line
CVE-2026-41940 isn’t theoretical. It’s not a “maybe patch this weekend” situation. It’s a pre-authentication, remote, root-level authentication bypass in software that runs on 1.5 million servers — and it’s already being weaponized by actors targeting governments and service providers. If you run cPanel and haven’t patched since April 28, treat your server as compromised until proven otherwise. Patch now. Rotate credentials now. Check your logs back to February. The internet is not being gentle about this one.

